In 2012, a young scam artist based in Asia
posing as a private investigator simply purchased the personal information for more than 200 million users directly from credit reporting giant Experian and then posted it for sale online. The only reason we know about the incident is that the U.S. Secret Service caught it. Experian didn’t.
Cyber criminals know that the weakest link in most computer networks is the people using it. Verizon’s highly respected
Data Breach Investigations Report has repeatedly noted that
most attacks start with employees. Attackers use “social engineering” to trick their victims into allowing unauthorized system access, data theft and even
specialized stealthy attacks used to quietly steal massive amounts of sensitive data over time. These attacks frequently exploit our natural tendency to want to help others. They can be in person, electronic or over the telephone, and there are a variety of ways they can be used to take advantage of you:
“Phishing” attacks are designed to steal your personal, financial or log-in information through an email, text message (referred to as “smishing”) or even an automated phone call (“vishing”). The attacks often appear to come from well-known and trusted companies like
banks,
airlines or
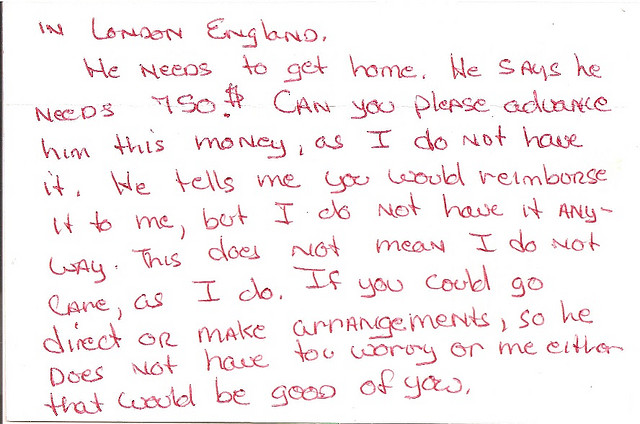
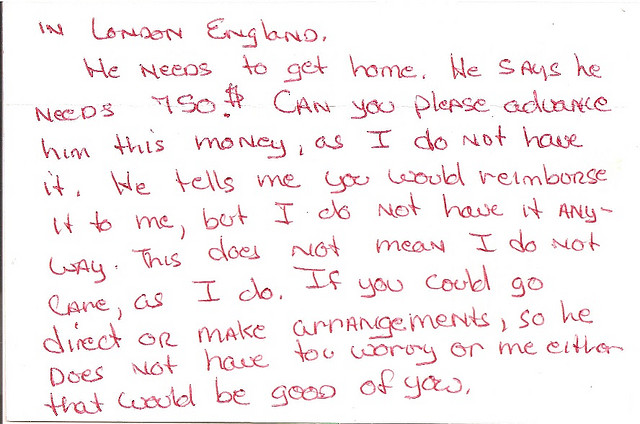
industry groups and contain attachments or links to websites that look legitimate but are really there to steal account log-in information or host malware ready to attack the recipient’s computer as soon as he clicks on any of the links. These emails and messages can also be used to lure victims into contact with scam artists posing as potential clients or officials offering to release substantial funds if only the target would be so kind as to hand over detailed personal information or a sum up front.
A
spear phishing email is a personalized version of a phishing attack looking for the weak link in an otherwise strong network. It will be aimed at a specific target (rather than a general phishing email intended to ensnare whoever falls for it) and typically includes personal or professional information to make the recipient trust the sender. These details can come from online sources like LinkedIn, Facebook and other social networks and contain information available via business-related websites, as well as particulars obtained directly from coworkers via social engineering.
Spear phishing emails often appear to come from a familiar source like a friend, family member, colleague or a business you deal with regularly. This is because of a process known as "spoofing," in which the actual sender hides his identity, and the “from” field in the email shows the fake sender’s name, not the real one.
The data breach at Forbes earlier this year
began with an early morning spear phishing attack against a senior executive.
Whaling is an attack that deliberately goes after senior executives, partners and other high-profile targets within a business. The idea behind this approach is that these targets are “big fish” who have wide access within the network yet may not take the precautions needed to keep their own accounts secure.
Pretexting is effectively in-person phishing to gain information or access to a restricted area. The term “pretexting” refers to the setup used to convince the target that there is a justifiable reason (or pretext) to divulge the information or access the person is after. These attacks can take a wide variety of forms, often revolving around someone (or a team) creating a distraction or masquerading as someone who could have legitimate access to the system they're targeting. It could be someone who claims to be from "corporate," a fake contractor,
fake IT personnel or something as random as a "fire inspector" allegedly checking the office for imagined safety hazards while an assistant/accomplice surreptitiously places devices to monitor or siphon sensitive data from the victim network.
Another in-person bit of trickery is
“tailgating.” That’s when someone who claims to have forgotten their company ID, etc. asks you to hold the door behind you, allowing him into a restricted area. The same term is also sometimes used to describe someone asking to briefly borrow your phone, tablet or laptop to check something quickly and actually downloading malware instead.
Live social engineering attacks can also come by phone, such as fake
“technical support” calls offering to fix imaginary problems with your computer if you will just allow the caller to briefly take control of it remotely.
Baiting is a type of attack in which a piece of portable electronic storage media like a CD-ROM, laptop or USB stick drive is left at or close to the target's workplace to tempt the curious victim into seeing what's on it. These will often include an official-looking logo or markings to make them especially tempting. How curious would you be to look at something labeled “Senior Executive Compensation – 2014” (with your company’s logo on it)? Of course, once the card, laptop or stick drive is connected, it will quietly download malware onto the network.
And, yes, this initial intrusion into the network will likely be traceable back to you.
What can you do to avoid being the weakest link? The one thing these attacks all have in common is that they rely on you to go along with the story they’re selling. The single best thing you can do whenever you receive an unsolicited electronic message or call from a business or someone you don’t know personally is to assume that it’s fake. Never click on links, open attachments, call phone numbers or use any other method of contact contained in any unsolicited emails, texts or calls. If you think the email, etc. could be legitimate, contact the alleged sender via phone or their official website.
If an email that appears to be from someone you know seems out of character, unexpected or strange in any way, give the sender a call to see if it really came from her.
When someone asks you to help her access something – or someplace – restricted, ask yourself
why she needs your help. Also, it never hurts to take a moment to check out the story you’re given. A quick phone call (not using a number she gives you) can derail a social engineering attack before it starts.
Tempting though it may be, opening that conveniently abandoned stick drive, etc. yourself is a bad idea. Take it to your company security or IT personnel.
Speaking of which, an IT department can (and should) take steps to help protect a network from electronic intruders, including the installation of
network security software, but don’t forget that the first line of defense against a social engineering attack is
you.