What is SERMP? An idea born out of the necessity when I needed a way to help my colleagues in the information technology security field explain to others in the organization the level of risk they faced and the progress being made in managing it.
IT security and ERM frameworks are numerous and readily available, but I wanted a way to bring the two together. After many editions and revisions, the Security Enterprise Risk Management Program, or SERMP, was born. The SERMP is a customized framework that creates a repeatable process that can be executed by non-IT professionals. Working with others in your organization, you form a team, develop a vision and scope and populate your customized framework tool overtime.
As an ERM practitioner, you don’t need to be an IT expert to be well-suited to implement a SERMP. You know how to identify and articulate risk, quantify or qualify the degree of risk and identify appropriate mitigations that can reduce uncertainty and create greater opportunity. In short, you are taking knowledge and skills that you use every day and applying them to a different environment.
SERMP is initiated to establish a model to assess, track and monitor all security risks and initiatives empirically and allows the organization to be confident that it is focused on the right things at the right time, and align new security risks and initiatives with the proper emphasis and investment. At its core, the SERMP is an enterprise risk management (ERM) model but expands upon the ERM model by incorporating a holistic framework approach, with strict emphasis on empirical support statements. This allows leadership to have very specific and targeted discussions regarding risk and impact with defensible data to support key decisions.
So, where do you start? Playing off the idea of crowdsourcing, you build your team based on the following characteristics:
#1 Willingness…
Okay, there are really no other characteristics needed. Because the SERMP framework breaks down IT security into components at a level that limits scope, and because it is repeatable, allowing for brief bursts of time commitment, the knowledge required to execute each segment is also reduced. If someone is willing to join the team and give of their time and has a desire to learn about IT security, they can contribute -- even better if they have some impact on IT security.
Many people have or should have an impact on IT security, but until engaged in SERMP may not even realize that they do.
Examples:
Facilities: physical security
Human Resources: access control and training
Communications: awareness and messaging
Risk Management: risk frameworks and cyber insurance
Procurement: contracts and vendor management
Project Managers: process documentation
Audit: frameworks and assurance
Compliance: governance and policy
It is highly recommended to have at least one IT security member on the SERMP team, but it is not required. The IT security staff (internal or external) will need to provide time to meet with SERMP team members, but they do not have to be working members of SERMP.
Anyone else willing to volunteer?
How much time is this going to take?
SERMP is about gathering and analyzing information over time. You can move quickly or slowly and expand or contract your scope as your resources allow, given the complexity of the IT structure and the organization's environment. I recommend doing small bursts of effort but on a regular basis:
- Initial introductory meeting to explain the concept (30 – 60 minutes)
- Planning meeting to develop a charter that includes vision and scope (1 – 2 hours)
- 30-minute meetings every two weeks with the SERMP team to discuss progress
- Quarterly report out to leadership and appropriate committees, i.e. risk or audit committee (30 minutes)
- Team-member monthly time commitment: five hours per team member to gather information, populate the framework and attend the 30-minute meetings
The above does not account for the time that you as the leader of the project will spend in oversight and administration, but because you control the pace and scope you can work the program into your schedule as time and resources permit.
Establishing a charter or similar document is helpful in having “recruiting” discussions for your SERMP team.
Example charter:
The Security Risk Management Program (SERMP) is initiated to establish a model to assess, track and monitor all security risks and initiatives empirically, and allows the organization to be confident that it is focused on the right things at the right time, and can add and align new security risks and initiatives with the proper emphasis and investment.
SERMP is a continuing program, but the major phases are:
- Establish Approach
- Enterprise Current State Assessment
- Risk Initiative Planning and Prioritization
- Risk and Initiative Progress: Quarterly reporting
- Annual Review
What are the challenges and issues we are trying to solve?
Security controls and investments were implemented without a measurable understanding of effectiveness or appropriateness. Have we invested our security dollars in the right places? Without a structured framework, we are guessing at worst, and at best have a siloed understanding of the security posture picture.
What are the goals of the program?
Establish a repeatable framework to:
- Confidently understand our current security posture
- Identify our key security risks and priorities
- Determine security remediation strategy
- Align remediation initiatives with strategy
- Establish empirical key risk indicators (KRIs) and key performance indicators (KPIs)
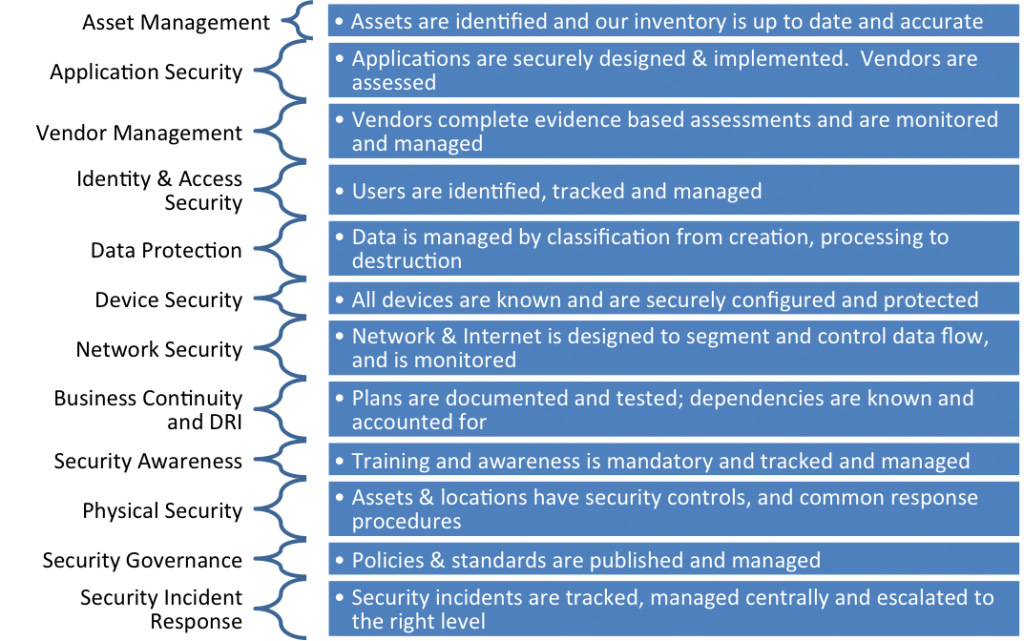
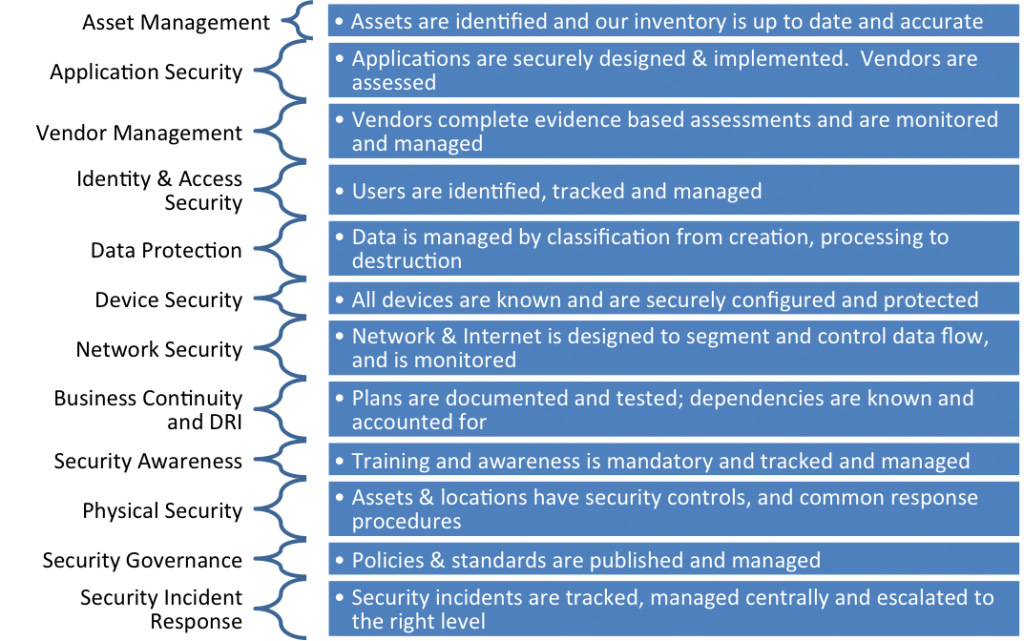
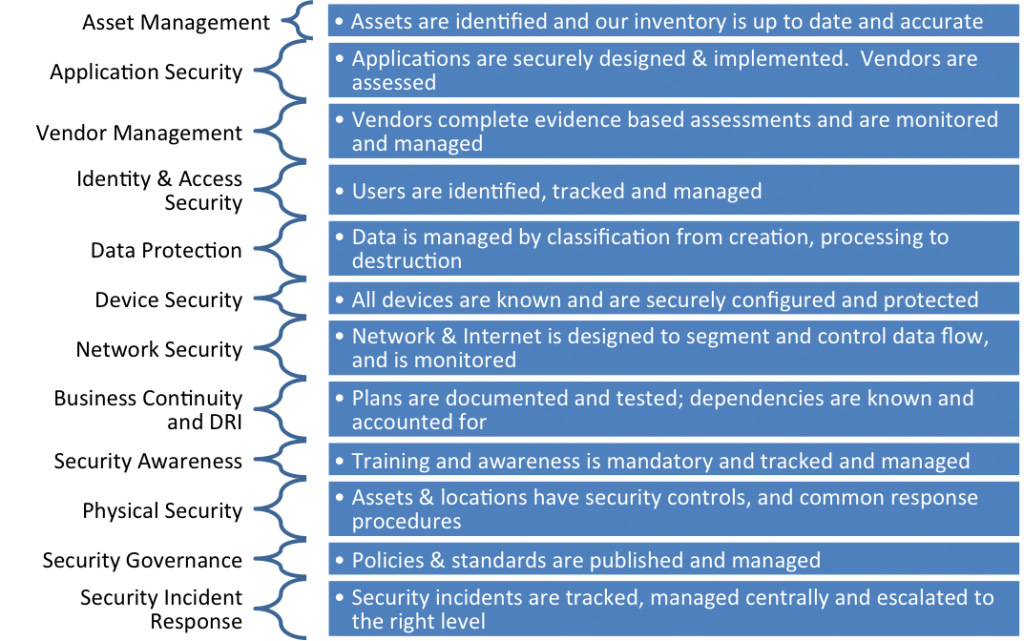
The complexity of security is organized into 12 separate domains (grounded in ISO 27000 but customized for the organization). Each domain has a lead, who is responsible for understanding the holistic posture of its scope, measure across the entire enterprise.
For each domain, there will be a strategy:
| Domain |
Details |
Description |
| Vision Value & Scope |
Scope & Definition |
|
| Policy Mapping |
Controls, Standards |
|
| Risk Assumptions |
Observations & Metrics |
|
| Metrics |
Baseline, KRI, KPI |
|
| Initiatives & Roadmap |
Initiatives, plan, 3 yr roadmap |
|
| Programs & Services |
What is in place |
|
| Partners |
Up & Downstream |
|
A reporting tool is used to track the SERMP, which houses the information for each domain, plus how the organization is managing the program: Establish, Assess, Treatment, Monitor, Review activities and Metric tracking for Risk Statement, Risk Impact, Key Risk Indicators(KRIs), Risk Remediation Initiatives, Current State (KPI), Target State (KRI) and Projects.
The reporting tool is used not only as a repository for information gathering but provides the team with a framework that breaks down the elements to be gathered and analyzed into manageable components. In the above charter, ISO 27000 is referenced, but other or multiple standards may be used.
 For each domain, there will be a strategy:
For each domain, there will be a strategy:
 For each domain, there will be a strategy:
For each domain, there will be a strategy:





